INTRODUCTION TO CRYPTOHACK
A fun, free platform for learning modern cryptography
register
KGYZ BGXOUAY SGYY SGSSGR
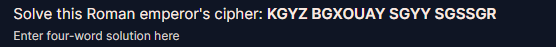
ceaser crypto
EAST VARIOUS MASS MAMMAL
INTRODUCTION TO CRYPTOHACK
This starter course gets you up and running with CryptoHack. You’ll learn to encode and decode data types that are commonly used in cryptography. Then you’ll get comfortable with the XOR operation which is at the centre of symmetric cryptography. Finally, the course ends with some fun XOR puzzles to test what you’ve learned.
CryptoHack is free to play and browse. If you need help or want to find out more details about the site, please first read the FAQ. If you want to interact with the community, check out the Discord chat linked on the sidebar.
Finding Flags
Each challenge is designed to help introduce you to a new piece of cryptography. Solving a challenge will require you to find a “flag”.
These flags will usually be in the format crypto{y0ur_f1rst_fl4g}. The flag format helps you verify that you found the correct solution.
Try submitting this flag into the form below to solve your first challenge.
|
|
Great Snakes
Modern cryptography involves code, and code involves coding. CryptoHack provides a good opportunity to sharpen your skills.
Of all modern programming languages, Python 3 stands out as ideal for quickly writing cryptographic scripts and attacks. For more information about why we think Python is so great for this, please see the FAQ.
Run the attached Python script and it will output your flag.
|
|
|
|
ASCII
ASCII is a 7-bit encoding standard which allows the representation of text using the integers 0-127.
Using the below integer array, convert the numbers to their corresponding ASCII characters to obtain a flag.
1[99, 114, 121, 112, 116, 111, 123, 65, 83, 67, 73, 73, 95, 112, 114, 49, 110, 116, 52, 98, 108, 51, 125]In Python, the
chr()function can be used to convert an ASCII ordinal number to a character (theord()function does the opposite).
|
|
|
|
Hex
When we encrypt something the resulting ciphertext commonly has bytes which are not printable ASCII characters. If we want to share our encrypted data, it’s common to encode it into something more user-friendly and portable across different systems.
Hexadecimal can be used in such a way to represent ASCII strings. First each letter is converted to an ordinal number according to the ASCII table (as in the previous challenge). Then the decimal numbers are converted to base-16 numbers, otherwise known as hexadecimal. The numbers can be combined together, into one long hex string.
Included below is a flag encoded as a hex string. Decode this back into bytes to get the flag.
163727970746f7b596f755f77696c6c5f62655f776f726b696e675f776974685f6865785f737472696e67735f615f6c6f747d
|
|
|
|
Base64
Another common encoding scheme is Base64, which allows us to represent binary data as an ASCII string using an alphabet of 64 characters. One character of a Base64 string encodes 6 binary digits (bits), and so 4 characters of Base64 encode three 8-bit bytes.
Base64 is most commonly used online, so binary data such as images can be easily included into HTML or CSS files.
Take the below hex string, decode it into bytes and then encode it into Base64.
172bca9b68fc16ac7beeb8f849dca1d8a783e8acf9679bf9269f7bf
|
|
|
|
Bytes and Big Integers
Cryptosystems like RSA works on numbers, but messages are made up of characters. How should we convert our messages into numbers so that mathematical operations can be applied?
The most common way is to take the ordinal bytes of the message, convert them into hexadecimal, and concatenate. This can be interpreted as a base-16/hexadecimal number, and also represented in base-10/decimal.
To illustrate:
message: HELLO ascii bytes: [72, 69, 76, 76, 79] hex bytes: [0x48, 0x45, 0x4c, 0x4c, 0x4f] base-16: 0x48454c4c4f base-10: 310400273487
Python’s PyCryptodome library implements this with the methods
bytes_to_long()andlong_to_bytes(). You will first have to install PyCryptodome and import it withfrom Crypto.Util.number import *. For more details check the FAQ.Convert the following integer back into a message:
111515195063862318899931685488813747395775516287289682636499965282714637259206269
|
|
|
|
XOR Starter
XOR is a bitwise operator which returns 0 if the bits are the same, and 1 otherwise. In textbooks the XOR operator is denoted by ⊕, but in most challenges and programming languages you will see the caret
^used instead.
A B Output 0 0 0 0 1 1 1 0 1 1 1 0 For longer binary numbers we XOR bit by bit:
0110 ^ 1010 = 1100. We can XOR integers by first converting the integer from decimal to binary. We can XOR strings by first converting each character to the integer representing the Unicode character.Given the string
label, XOR each character with the integer13. Convert these integers back to a string and submit the flag ascrypto{new_string}.The Python
pwntoolslibrary has a convenientxor()function that can XOR together data of different types and lengths. But first, you may want to implement your own function to solve this.
|
|
|
|
XOR Properties
In the last challenge, you saw how XOR worked at the level of bits. In this one, we’re going to cover the properties of the XOR operation and then use them to undo a chain of operations that have encrypted a flag. Gaining an intuition for how this works will help greatly when you come to attacking real cryptosystems later, especially in the block ciphers category.
There are four main properties we should consider when we solve challenges using the XOR operator
Commutative: A ⊕ B = B ⊕ A Associative: A ⊕ (B ⊕ C) = (A ⊕ B) ⊕ C Identity: A ⊕ 0 = A Self-Inverse: A ⊕ A = 0
Let’s break this down. Commutative means that the order of the XOR operations is not important. Associative means that a chain of operations can be carried out without order (we do not need to worry about brackets). The identity is 0, so XOR with 0 “does nothing”, and lastly something XOR’d with itself returns zero.
Let’s put this into practice! Below is a series of outputs where three random keys have been XOR’d together and with the flag. Use the above properties to undo the encryption in the final line to obtain the flag.
KEY1 = a6c8b6733c9b22de7bc0253266a3867df55acde8635e19c73313 KEY2 ^ KEY1 = 37dcb292030faa90d07eec17e3b1c6d8daf94c35d4c9191a5e1e KEY2 ^ KEY3 = c1545756687e7573db23aa1c3452a098b71a7fbf0fddddde5fc1 FLAG ^ KEY1 ^ KEY3 ^ KEY2 = 04ee9855208a2cd59091d04767ae47963170d1660df7f56f5faf
Before you XOR these objects, be sure to decode from hex to bytes.
|
|
|
|
Favourite byte
For the next few challenges, you’ll use what you’ve just learned to solve some more XOR puzzles.
I’ve hidden some data using XOR with a single byte, but that byte is a secret. Don’t forget to decode from hex first.
173626960647f6b206821204f21254f7d694f7624662065622127234f726927756d
|
|
|
|
You either know, XOR you don’t
I’ve encrypted the flag with my secret key, you’ll never be able to guess it.
Remember the flag format and how it might help you in this challenge!
10e0b213f26041e480b26217f27342e175d0e070a3c5b103e2526217f27342e175d0e077e263451150104
|
|
guess key is myXORkey
|
|
|
|